- Liittynyt
- 20.10.2016
- Viestejä
- 7 026
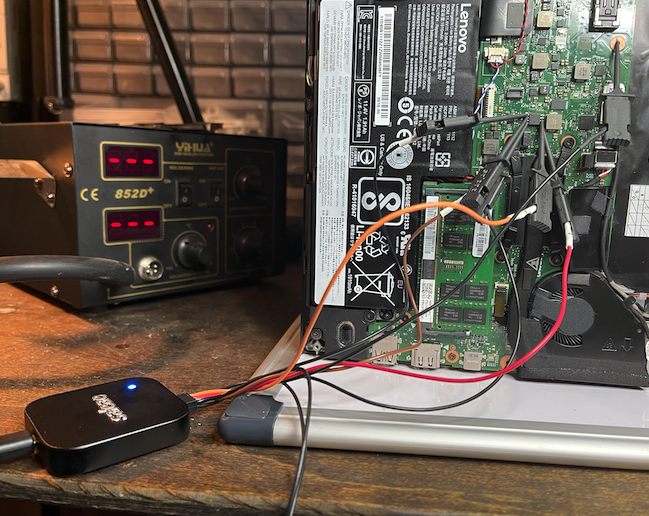
Eipä se TPM nyt sitten olekaan niin kauhean turvallinen, kuin annetaan ymmärtää, tottakai tämä hyökkäys vaatii todellakin fyysisen pääsyn koneelle, mutta monesti juurikin läppäri pöllitään ja sillä selvä. Tietenkin tämä on isompi vaara tuolla liike-elämä sun muissa ympäristöissä, jossa liikkuu rahaa pikkasen enemmän kuin jonkun yksityisen nörtin koneen sisällön takana. Mutta tämähän siis vaikka mahdollistaa viranomaisten pääsyn koneelle yllättävän helposti, jos epäillään sisältävän jotain laitonta jne...
 dolosgroup.io
The laptop was locked down well, with full disk encryption via a Trusted Platform Module (TPM) and Bitlocker being the cherry on top.
dolosgroup.io
The laptop was locked down well, with full disk encryption via a Trusted Platform Module (TPM) and Bitlocker being the cherry on top.
The laptop wasn’t configured to require a password or PIN to boot (default for BitLocker). In this configuration, the TPM automatically sends the encryption key to the boot loader during boot. This key is sent over an SPI interface in plaintext. All that is needed is to probe the SPI bus during boot. While the TPM is physically small enough to make this quite difficult, the SPI interface is a bus, meaning that it connects to multiple chips on the board. One of which is a CMOS chip, with much larger pins. The capture was successful, and they soon had access to the filesystem on the encrypted drive.
A pre-equipped attacker can perform this entire attack chain in less than 30 minutes with no soldering, simple and relatively cheap hardware, and publicly available tools.
From Stolen Laptop to Inside the Company Network — Dolos Group
What can you do with a stolen laptop? Can you get access to our internal network? That was the question a client wanted answered recently. Spoiler alert: Yes, yes you can. This post will walk you through how we took a “stolen” corporate laptop and chained several exploits together to get inside the
The laptop wasn’t configured to require a password or PIN to boot (default for BitLocker). In this configuration, the TPM automatically sends the encryption key to the boot loader during boot. This key is sent over an SPI interface in plaintext. All that is needed is to probe the SPI bus during boot. While the TPM is physically small enough to make this quite difficult, the SPI interface is a bus, meaning that it connects to multiple chips on the board. One of which is a CMOS chip, with much larger pins. The capture was successful, and they soon had access to the filesystem on the encrypted drive.
A pre-equipped attacker can perform this entire attack chain in less than 30 minutes with no soldering, simple and relatively cheap hardware, and publicly available tools.










/cloudfront-us-east-2.images.arcpublishing.com/reuters/N45WXQTJYFIIBNBHNKPEHHVXO4.jpg)


 Ja 99% näistä ongelmista on windows-käyttäjillä, meillä on linuxia käyttäviä ihmisiäkin mutta niiltä ei juurikaan tule kysymyksiä tai sitten ne ovat ihan oikeasti aiheellisia.
Ja 99% näistä ongelmista on windows-käyttäjillä, meillä on linuxia käyttäviä ihmisiäkin mutta niiltä ei juurikaan tule kysymyksiä tai sitten ne ovat ihan oikeasti aiheellisia.